Peculiar.behaviour.7z [OFFICIAL]
The file is a known malware sample frequently used in cybersecurity training, CTF (Capture The Flag) competitions, and malware analysis labs . It is not a standard document or media file; it is a compressed archive containing malicious code designed for study or exploitation. 🛡️ Technical Overview File Type : 7-Zip Compressed Archive ( .7z ).
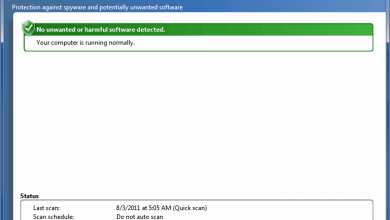
: It may create a Scheduled Task or add an entry to HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run . 3. Indicators of Compromise (IoCs)
Always use a (e.g., Any.Run, Flare-VM). Ensure the VM is isolated from your local network. Peculiar.Behaviour.7z
: Requires the user to manually extract the .7z file, often using a password provided in the email (e.g., infected or 1234 ). 2. Execution Flow
: Often involves Process Injection , Persistence via Registry keys, or C2 (Command & Control) communication. 🔍 Detailed Analysis Report 1. Delivery Method The file is a known malware sample frequently
Do you have the of the specific file you are looking at?
Did you find this in a or a training lab ? : It may create a Scheduled Task or
: Look for unusual .exe or .dll files in temporary directories.